IOS Hit With Another Asian Malware Outbreak
The researchers at Palo Alto Networks are working overtime thanks to plenty of new mobile exploits creeping up seemingly every day. There have no comments released by Apple regarding the malwares. This means everyone owning an iPhone could be at risk of being infected.
Moreover, even though as we’ve seen all throughout the XcodeGhost saga, apps downloaded from the iOS App Store are not always clean, one should also only download applications from the App Store to decrease the chance of installing malware ridden apps.
As a substitute, enterprises are allowed to signal their apps with digital certificates that confirm their id – the precise firm, for example – which the machine checks earlier than permitting set up. “WireLurker proved that non-jailbroken iOS devices can also be infected through abuse of the enterprise distribution mechanism”.
What’s unique about YiSpecter, said Olson, was that it paired the enterprise certificate tactic with one previously discussed only by academics.
Private APIs are those Apple keeps close to its vest.
However, the YiSpecter uses private APIs to attack sensitive functionalities of the iOS.
“Three of the malicious components use tricks to hide their icons from iOS’ SpringBoard, which prevents the user from finding and deleting them“, Xiao said.
YiSpecter is the malware’s name, and messing with iOS apps is its game. But users, faced only with a pop-up that asked them to click to continue downloading and installing such an app, typically breezed by the warning.
Like most malware, it originally appealed to those with prurient interests.
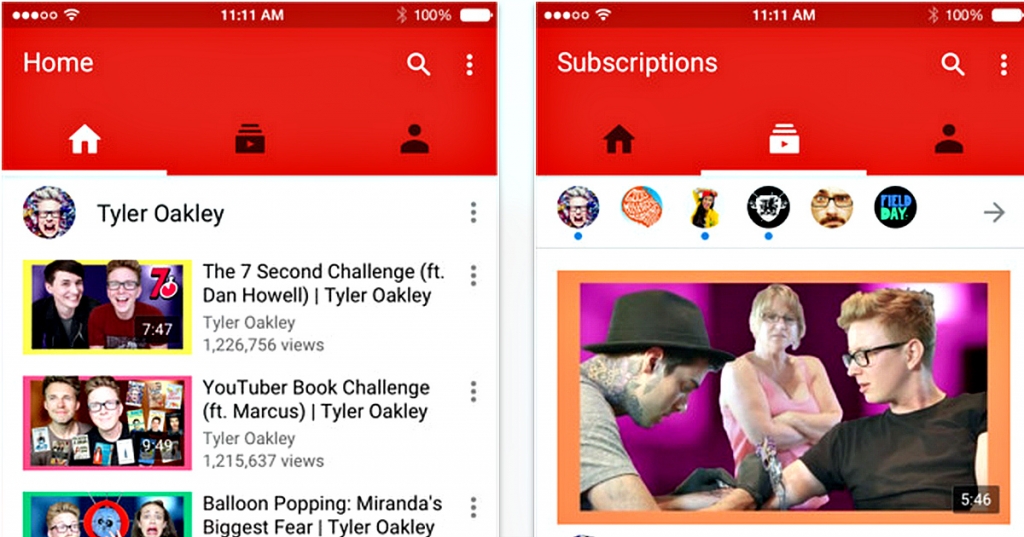
To start the process, download the Move to iOS app on your Android phone. It’ll replace certain legitimate apps it finds with infected versions, serve full-screen pop-up ads that appear when certain apps are launched, and fire up an HTTP server that listens for instructions and pulls down additional payloads when required. YiSpecter is the latest form of malware to slip through Apple’s security mazes, and could end up being a disastrous hit for the company in the Chinese and Taiwanese markets. Is iOS still a secure operating system? It’s a good idea to conduct proper research before accepting an upgrade so you know what you’re in for. Within the paper, the researchers examined greater than 2,000 iOS apps within the App Retailer and located that nearly a hundred and fifty – or about 7% – used personal APIs. Apple says it has since fixed the issue with iOS 9.0.2.
Luca Todesco, a long-time jailbreaker, has released the iOS 8.4.1 jailbreak solution last Friday and though it is efficient amateur users might not be able to comprehend Todesco’s system yet. Because of that difficulty, Olson anxious that malware abusing private APIs demonstrated to such effect by YiSpecter, would proliferate.
“For a very long time, Apple’s “walled backyard” labored extraordinarily properly”, Olson stated.
Additionally, Apple has introduced a new way of intuitively navigating with iOS 9’s 3D touch.
In many cases much of the extra content won’t be needed.